The Testimony That Changed Everything
On March 25, 2026, CISA Director Sean Plankey sat before the Senate Homeland Security and Governmental Affairs Committee and delivered testimony that should alarm every compliance officer, CISO, and risk manager in the country.
The numbers were stark. Roughly 60% of CISA’s workforce has been furloughed, reassigned, or separated under the Department of Government Efficiency (DOGE) restructuring initiative. The agency that serves as America’s primary civilian cybersecurity authority — the organization that maintains the Known Exploited Vulnerabilities catalog, coordinates sector-specific threat intelligence, and issues the advisories your compliance program almost certainly relies on — is now operating in what Plankey himself characterized as a “reactive posture.”
Let that phrase sink in. Reactive. Not proactive. Not anticipatory. Not resilient. Reactive.
For an agency whose entire reason for existence is to get ahead of threats before they become breaches, “reactive” is not a temporary inconvenience. It is a fundamental inversion of mission. And for the thousands of organizations across critical infrastructure sectors that have built their compliance programs on the assumption that CISA would be there — publishing timely advisories, updating vulnerability catalogs, coordinating sector-level threat intelligence — this shift represents an operational crisis that demands immediate action.
What “Reactive Posture” Actually Means in Practice
To understand the compliance implications, you first need to understand what CISA is no longer doing. A reactive posture is not merely a slower version of the proactive one. It represents the elimination of entire categories of activity that compliance programs have come to depend on.
Proactive Threat Hunting: Gone
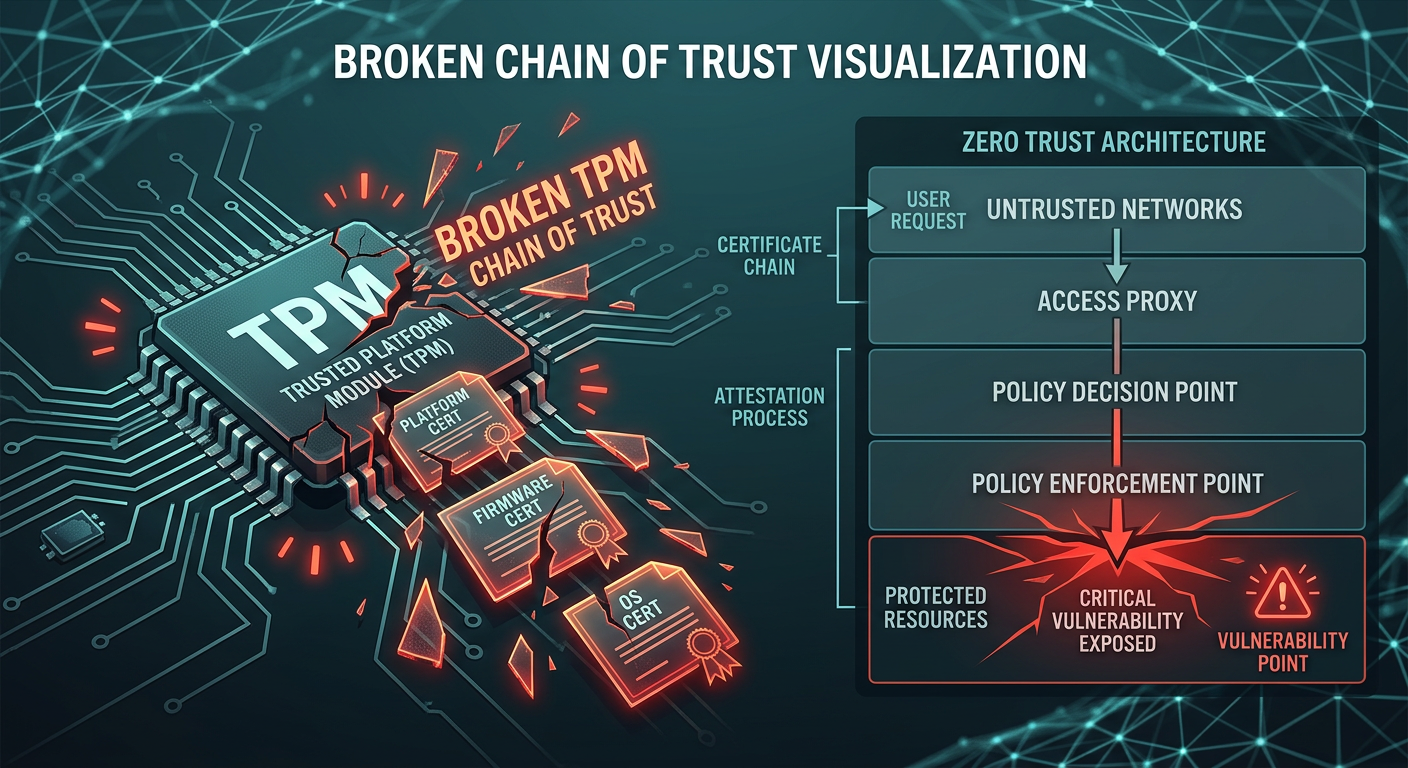
CISA’s threat hunting teams — the analysts who actively search for indicators of compromise across federal networks and coordinate with critical infrastructure operators — have been decimated. Before the cuts, CISA operated joint cyber defense collaborative (JCDC) engagements that brought government and private sector teams together to hunt for advanced persistent threats before they escalated into incidents. These operations required experienced analysts with deep technical expertise and established relationships across sectors.
Those analysts are among the 60% who are no longer at their desks.
What remains is an agency that can respond to reported incidents but can no longer identify emerging threats before they reach your environment. The difference between hunting for threats and waiting for them to arrive is the difference between finding a vulnerability in your network on your terms and discovering it during an active breach on the attacker’s terms.
Slower Advisories and Alerts
CISA’s advisory pipeline — the ICS-CERT advisories, cybersecurity alerts, and joint advisories published in coordination with the FBI, NSA, and international partners — has visibly slowed. Analysis of CISA’s public advisory feed shows a measurable decline in both the volume and the specificity of published guidance since the workforce reductions began.
For compliance teams that reference CISA advisories to inform patch prioritization, risk assessments, and board reporting, this delay creates a dangerous gap. Threats do not wait for advisories. A vulnerability actively exploited in the wild is just as dangerous whether CISA has published guidance about it or not. But without timely, authoritative guidance from CISA, organizations relying on the agency as their primary source of threat intelligence are flying partially blind.
Sector Coordination: Fractured
Perhaps the most consequential loss is in sector-specific coordination. CISA served as the nexus point connecting Information Sharing and Analysis Centers (ISACs), sector risk management agencies (SRMAs), and critical infrastructure operators. This coordination infrastructure — built over years through the cultivation of trust, relationships, and shared operational processes — cannot be maintained on a skeleton crew.
Healthcare ISACs, financial sector ISACs, energy ISACs, and water sector ISACs all relied on CISA as a central coordination hub for cross-sector threat intelligence. When a threat actor targeting the healthcare sector pivots to financial services, CISA was the entity that connected those dots. With 60% of that connective tissue severed, sectors are increasingly operating in silos — aware of threats within their own verticals but blind to the cross-sector campaigns that sophisticated adversaries routinely execute.
The KEV Catalog: Your Compliance Baseline Is Eroding
If you work in compliance, you almost certainly reference CISA’s Known Exploited Vulnerabilities (KEV) catalog. Introduced in 2021 through Binding Operational Directive 22-01, the KEV catalog has become the de facto standard for vulnerability prioritization across both federal agencies and private sector organizations.
The KEV catalog’s value was never just the list itself — it was the rigorous, expert-driven process behind it. CISA analysts reviewed intelligence reports, confirmed active exploitation, assessed the scope and impact of each vulnerability, and made authoritative decisions about what belonged on the list. That curation process required deep technical expertise and constant monitoring of the threat landscape.
With reduced staffing, the KEV catalog update cadence has already slowed. Vulnerabilities that would previously have been added within days of confirmed exploitation are now taking longer to appear. For organizations that use the KEV catalog as a primary input to their vulnerability management programs — and many compliance frameworks effectively require this — the implications are immediate:
- Patch prioritization gaps: If a vulnerability is being actively exploited but has not yet been added to the KEV catalog, organizations relying solely on KEV for prioritization may not patch it in time.
- Compliance documentation risk: Auditors and regulators who have come to accept “we follow the KEV catalog” as evidence of a robust vulnerability management program may begin questioning whether that is sufficient.
- False sense of security: The absence of a vulnerability from the KEV catalog has never meant the vulnerability is not being exploited. But with slower updates, the gap between reality and the catalog widens.
SHIELDS UP in Name Only
In early 2022, CISA launched the SHIELDS UP campaign in response to the Russia-Ukraine conflict, urging organizations to adopt a heightened cybersecurity posture. The initiative provided concrete, actionable guidance for organizations of all sizes — from patch management checklists to incident response preparation steps.
SHIELDS UP became a touchstone for compliance programs. Risk managers referenced it in board presentations. CISOs used it to justify budget requests. Compliance teams cited it in audit responses.
But SHIELDS UP was never a static document. Its value lay in continuous updates — new threat intelligence folded into actionable guidance, sector-specific supplements, and direct engagement with organizations implementing the recommendations. With 60% of the workforce gone, SHIELDS UP has become a static artifact rather than a living program. The guidance remains on CISA’s website, but the team that maintained, updated, and operationalized it has been gutted.
Organizations that point to SHIELDS UP compliance in their risk registers should be asking: compliance with what version? The 2022 original? The 2024 update? And who is maintaining the threat intelligence that informed those recommendations?
Frameworks Under Pressure: NIST CSF, FISMA, and Critical Infrastructure Standards
The ripple effects of CISA’s reduced capacity extend far beyond the agency’s own programs. Multiple compliance frameworks depend on CISA as a critical input, and the degradation of CISA’s capabilities creates compounding risks across the regulatory landscape.
NIST Cybersecurity Framework (CSF)
NIST CSF 2.0, released in 2024, explicitly incorporates references to CISA resources throughout its guidance. The framework’s Identify, Protect, Detect, Respond, and Recover functions all reference threat intelligence, vulnerability management, and incident coordination activities that CISA has historically provided.
Organizations that have mapped their compliance programs to NIST CSF and relied on CISA resources to fulfill specific control requirements now face a gap. The framework has not changed, but the ecosystem of free, authoritative resources that supported its implementation has contracted significantly.
FISMA and Federal Compliance
For federal agencies and their contractors, the implications are even more direct. The Federal Information Security Modernization Act (FISMA) establishes cybersecurity requirements that are operationally dependent on CISA. Binding Operational Directives — including BOD 22-01 (KEV catalog), BOD 23-01 (asset visibility), and BOD 25-01 (secure cloud configuration) — are issued and enforced by CISA.
With reduced capacity, CISA’s ability to issue new BODs, provide implementation guidance for existing ones, and conduct compliance assessments is materially diminished. Federal contractors and IT service providers that serve government clients should anticipate uncertainty in compliance expectations and prepare for the possibility that enforcement mechanisms may be inconsistent.
Critical Infrastructure Sector-Specific Frameworks
Each of the 16 critical infrastructure sectors has its own regulatory landscape, and many of those frameworks rely heavily on CISA coordination. The electricity subsector’s NERC CIP standards, the water sector’s America’s Water Infrastructure Act requirements, the healthcare sector’s HIPAA Security Rule — all of these frameworks operate more effectively when CISA is actively coordinating threat intelligence and publishing sector-specific guidance.
The loss of sector-specific CISA analysts means less tailored guidance, fewer joint advisories addressing threats unique to individual sectors, and reduced capacity for the kind of direct engagement that translates generic cybersecurity best practices into sector-specific compliance actions.
The Political Context: Brief and Factual
Understanding the current situation requires acknowledging its origins without veering into partisan commentary. The facts are straightforward.
The Department of Government Efficiency (DOGE), established through executive order in early 2025, was tasked with identifying cost reductions across the federal government. CISA, housed within the Department of Homeland Security, was identified as an agency with potential for significant workforce reduction.
The resulting cuts — through a combination of furloughs, voluntary separations, reductions in force, and non-renewal of contracts — reduced CISA’s operational workforce by approximately 60%. The reductions were not evenly distributed; some divisions, particularly those focused on election security and mis/disinformation, were more heavily impacted. But operational cybersecurity teams, including threat analysts, vulnerability researchers, and sector coordinators, were also significantly affected.
Director Sean Plankey, who assumed leadership of the agency in an acting capacity following the departure of previous leadership, has publicly acknowledged the workforce challenges while defending the agency’s core mission. His March 25 testimony described an agency that remains committed to its mission but is operating with fundamentally reduced capacity.
Several senior CISA officials have departed the agency. Institutional knowledge — the kind of deep expertise that takes years to develop and cannot be replaced by hiring — has walked out the door. Rebuilding that capability, even if funding were restored immediately, would take years.
The Budget Reality: What CISA Provided for Free, You Now Fund Yourself
Here is the uncomfortable financial conversation that every CISO and CFO needs to have in the next 30 days.
CISA provided an enormous amount of cybersecurity capability to the private sector at no direct cost. Threat intelligence feeds. Vulnerability scanning services (including the Cyber Hygiene program). Incident response assistance. Sector coordination. Advisory publications. Training and tabletop exercises.
Organizations that consumed these services — and many did without fully appreciating their value — now need to replace them. The market costs are not trivial:
| CISA Service (Previously Free) | Commercial Replacement | Estimated Annual Cost |
|---|---|---|
| KEV-equivalent threat intel feeds | Recorded Future, Mandiant, CrowdStrike Falcon Intelligence | $50,000–$250,000 |
| Vulnerability scanning (Cyber Hygiene) | Qualys, Tenable, Rapid7 | $25,000–$150,000 |
| Incident response support | Retainer with Mandiant, CrowdStrike, Secureworks | $100,000–$500,000 |
| Sector-specific threat briefings | Industry-specific threat intel subscriptions | $30,000–$100,000 |
| Tabletop exercises and training | Third-party consulting firms | $15,000–$75,000 per exercise |
For a mid-sized enterprise, replacing even a fraction of what CISA provided could add $200,000 to $500,000 in annual cybersecurity spending. For smaller organizations — the ones least able to absorb the cost — the gap may simply go unfilled.
Compliance officers should be preparing budget justifications now. The conversation with leadership is straightforward: the federal government is no longer providing capabilities we depended on, and we must fund alternatives or accept materially increased risk.
Five Things to Do Right Now If You Relied on CISA
The time for waiting and hoping for a reversal is over. Whether CISA’s capacity is eventually restored or not, the gap exists today, and compliance programs that rely on CISA resources are exposed today. Here is your action plan.
1. Audit Your CISA Dependencies
Most organizations do not have a clear picture of how deeply CISA resources are embedded in their compliance programs. Conduct an immediate audit:
- Threat intelligence: Are CISA advisories, alerts, or the KEV catalog referenced in your vulnerability management policy? In your risk assessment methodology? In your board reporting?
- Incident response: Does your IR plan assume CISA assistance? Do your tabletop exercises include CISA coordination as a step?
- Compliance controls: Have you mapped specific compliance controls to CISA resources? Which controls are affected if those resources degrade or disappear?
- Training and awareness: Does your security awareness program reference CISA materials?
Document every dependency. Assign an owner to each one. Establish a timeline for mitigation.
2. Diversify Your Threat Intelligence Sources
If CISA was your primary or sole source of threat intelligence, you are already behind. Establish a multi-source intelligence capability immediately:
- Commercial feeds: Subscribe to at least one commercial threat intelligence platform (Recorded Future, Mandiant Threat Intelligence, CrowdStrike Falcon X, or equivalent).
- ISAC membership: If you are not already an active member of your sector’s ISAC, join immediately. ISACs are becoming more important as CISA’s coordination role diminishes.
- Open-source intelligence: Integrate OSINT feeds (AlienVault OTX, Abuse.ch, MITRE ATT&CK updates) into your monitoring.
- Peer networks: Establish or strengthen informal intelligence-sharing relationships with peer organizations in your sector.
- International sources: NCSC (UK), ACSC (Australia), CCCS (Canada), and BSI (Germany) all publish high-quality advisories. Diversify your geographic sources.
3. Accelerate Your Vulnerability Management Program
With the KEV catalog potentially lagging, your vulnerability management program needs to be more sophisticated, not less. Take these steps:
- Add exploitation intelligence sources: Supplement KEV with data from Exploit-DB, GreyNoise, Shadowserver, and vendor-specific advisories.
- Implement risk-based prioritization: Move beyond CVSS scores. Use EPSS (Exploit Prediction Scoring System) and SSVC (Stakeholder-Specific Vulnerability Categorization) to prioritize vulnerabilities based on actual exploitation likelihood.
- Reduce mean time to patch: If your current patching SLA is 30 days for critical vulnerabilities, challenge yourself to cut it to 14 days. The window of exposure is widening as advisory timelines stretch.
- Automate where possible: Automated patch deployment for commodity systems frees your limited security team to focus on the complex patching decisions that require human judgment.
4. Update Your Compliance Documentation
Your compliance program documentation almost certainly contains references to CISA resources that are no longer reliable. Update proactively:
- Risk assessments: Add a new risk entry: “Reduced federal cybersecurity support capabilities.” Quantify the impact using the budget estimates above.
- Vulnerability management policies: Replace single-source KEV references with multi-source intelligence requirements.
- Incident response plans: Remove assumptions about CISA assistance timelines. Ensure your IR plan functions independently.
- Board reporting: Prepare a briefing for your board or audit committee on the CISA situation and your mitigation plan. Boards that learn about this from a news headline rather than from their CISO will be asking uncomfortable questions.
- Audit evidence: Proactively engage with your auditors about changes to your threat intelligence sources. It is better to explain the transition now than to defend a gap during an audit.
5. Strengthen Internal Capabilities
The strategic lesson of the CISA situation is that dependence on any single external entity — whether government or commercial — creates unacceptable concentration risk. Use this moment to invest in internal capabilities that reduce external dependence:
- Hire or upskill threat analysts: Even one dedicated threat intelligence analyst who can curate and contextualize multi-source intelligence is transformative for a mid-sized organization.
- Build internal playbooks: Document the threat intelligence workflows that CISA advisories used to trigger. Ensure those workflows can execute with alternative inputs.
- Invest in detection engineering: Write detection rules for the TTPs (Tactics, Techniques, and Procedures) that CISA advisories previously highlighted. Use the MITRE ATT&CK framework to structure your detection coverage.
- Conduct your own exercises: Do not wait for CISA-facilitated tabletop exercises. Run your own. Quarterly at minimum. Include scenarios that specifically address the loss of federal cybersecurity support.
The Compliance Checklist: Your 30-Day Action Plan
For the compliance officer who needs a concrete, time-bound plan to present to leadership, here is your 30-day roadmap:
Week 1: Assessment
- Complete CISA dependency audit across all compliance controls
- Identify all policies and procedures that reference CISA resources
- Brief CISO and executive leadership on the situation and immediate risks
Week 2: Sourcing
- Evaluate and select at least two commercial threat intelligence sources
- Confirm or establish ISAC membership and engagement
- Subscribe to international partner advisory feeds (NCSC, ACSC, CCCS)
Week 3: Documentation
- Update vulnerability management policy to reflect multi-source intelligence
- Revise incident response plan to remove CISA assistance assumptions
- Update risk register with reduced federal cybersecurity support risk entry
Week 4: Implementation and Communication
- Integrate new intelligence sources into monitoring and alerting workflows
- Prepare and deliver board-level briefing on CISA impact and mitigation
- Submit budget request for commercial replacements of CISA services
- Schedule next tabletop exercise incorporating new intelligence sources
Looking Ahead: The New Normal
It is tempting to view the CISA situation as temporary — a political pendulum that will eventually swing back. And perhaps it will. But compliance programs cannot be built on hope, and prudent risk management demands that organizations plan for the current reality, not the one they wish existed.
The deeper lesson is structural. For too long, the cybersecurity community treated CISA as a kind of free infrastructure — always available, always reliable, always there. We embedded dependencies on it into our programs without fully accounting for the concentration risk. We referenced it in policies without building fallback capabilities. We consumed its intelligence without investing in our own analytical capacity.
That model was always fragile. Now it is broken.
The organizations that will navigate this transition most effectively are the ones that treat it not as a crisis but as a catalyst — an opportunity to build more resilient, more self-sufficient compliance programs that can operate effectively regardless of the federal government’s cybersecurity posture.
The threats have not diminished. Nation-state actors, ransomware operators, and cybercriminal enterprises are not observing a pause while CISA reorganizes. If anything, sophisticated adversaries will view this moment as an opportunity — a window in which their targets are less informed, less coordinated, and less prepared.
Your compliance program must not be among them.
This analysis is based on publicly available testimony, government publications, and industry reporting as of March 27, 2026. Organizations should consult with qualified legal and cybersecurity professionals for guidance specific to their regulatory obligations and risk profile.