Executive Summary
On February 6, 2026, a critical vulnerability was disclosed in Keylime, a CNCF (Cloud Native Computing Foundation) project used for remote attestation in zero-trust architectures. The vulnerability, tracked as CVE-2026-1709, is an authentication bypass that allows unauthenticated attackers to perform administrative operations on Keylime registrars—the core component responsible for validating the trustworthiness of systems in a zero-trust environment.
The irony is profound: The system designed to verify trust can no longer be trusted.
Keylime is deployed in environments that take security seriously—government agencies, critical infrastructure, defense contractors, and enterprises implementing zero-trust architectures. These organizations chose Keylime specifically because they needed hardware-rooted cryptographic verification of system integrity. They needed to ensure that systems hadn’t been compromised before granting them network access.
CVE-2026-1709 undermines that entire model. An attacker with network access to a Keylime registrar can bypass authentication and:
- Register malicious systems as trusted
- Modify attestation policies to allow compromised systems
- Disable attestation for specific systems
- Exfiltrate sensitive attestation data and cryptographic keys
For compliance officers, security architects, and risk managers, this vulnerability represents a fundamental compromise of trust infrastructure—the foundational layer upon which zero-trust architectures are built.
Understanding Keylime: The Foundation of Hardware-Rooted Trust
Before diving into the vulnerability, it’s essential to understand what Keylime does and why it matters.
What Is Remote Attestation?
Remote attestation is a security mechanism that allows one system (the verifier) to determine the trustworthiness of another system (the attested node) before granting it access to resources or networks.
The Core Idea: Rather than trusting a system because it has correct credentials (username/password, certificate), attestation verifies that the system’s hardware and software are in a known-good state.
How It Works:
- Measurement: The system boots, and each component (firmware, bootloader, kernel, applications) is cryptographically measured
- Storage: Measurements are stored in a hardware Trusted Platform Module (TPM)
- Reporting: The system reports its measurements to an attestation service
- Verification: The attestation service compares measurements to known-good values
- Decision: Based on verification, the system is granted or denied access
Why This Matters: Traditional authentication verifies who is accessing resources. Attestation verifies what is accessing resources. Even if an attacker has valid credentials, a compromised system with modified measurements would fail attestation and be denied access.
What Is Keylime?
Keylime is an open-source implementation of remote attestation that:
- Scales to thousands of nodes
- Leverages TPM hardware for cryptographic root of trust
- Provides continuous runtime integrity monitoring (not just boot-time)
- Integrates with Kubernetes and cloud-native environments
Key Components:
1. Agent (keylime-agent):
- Runs on each node being attested
- Interfaces with TPM hardware
- Reports measurements to the verifier
2. Verifier (keylime-verifier):
- Requests attestation from agents
- Compares measurements to policies
- Makes trust decisions
3. Registrar (keylime-registrar):
- Maintains registry of all nodes
- Stores public attestation keys
- Performs initial node enrollment
- Critical component compromised by CVE-2026-1709
4. Tenant (keylime-tenant):
- Command-line tool for administrators
- Registers nodes for attestation
- Defines attestation policies
Where Keylime Is Deployed
Keylime is used in security-critical environments:
Government and Defense:
- Federal agencies requiring high assurance
- Defense contractors protecting classified systems
- Intelligence community protecting sensitive operations
Critical Infrastructure:
- Energy sector protecting SCADA systems
- Telecommunications protecting network infrastructure
- Financial services protecting high-value systems
Cloud and Edge:
- Kubernetes clusters requiring node attestation
- Edge computing deployments in untrusted physical locations
- Multi-tenant cloud environments requiring tenant isolation
Zero-Trust Implementations:
- Enterprises moving to zero-trust architecture
- Organizations requiring continuous verification
- Environments with high insider threat risk
CVE-2026-1709: Anatomy of the Vulnerability
The Technical Details
CVE-2026-1709: Keylime Registrar Authentication Bypass
Severity: Critical (CVSS score likely 9.0+)
Component: keylime-registrar
Affected Versions: Keylime 7.12.0 and later
Status: Patched in version 7.12.1-11
Vulnerability Description: The Keylime registrar, since version 7.12.0, does not enforce client-side TLS authentication. This means that mutual TLS (mTLS)—the mechanism that should require clients to present valid certificates to authenticate—is not functioning.
What This Means: Any attacker with network access to the registrar can connect and perform administrative operations without providing credentials or certificates. The registrar accepts connections from any source and processes their requests as if they were authenticated.
Root Cause: A code change in version 7.12.0 accidentally disabled the mTLS verification that authenticated clients connecting to the registrar. This appears to be an unintentional regression rather than a deliberate backdoor.
The Attack Scenario
1. Discovery Phase: Attacker scans for Keylime registrars on the network (typically port 8891):
nmap -p 8891 target-network
2. Connection Phase: Attacker connects to registrar without valid client certificate:
# This should fail but succeeds due to CVE-2026-1709
curl -k https://registrar:8891/agents/
3. Exploitation Phase: Attacker performs unauthorized administrative operations:
Register Malicious Nodes:
# Register a compromised system as trusted
curl -X POST https://registrar:8891/agents/malicious-uuid \
-d '{"aik":"<attacker-controlled-key>"}'
Modify Existing Registrations:
# Change attestation keys for existing nodes
curl -X PUT https://registrar:8891/agents/legitimate-uuid \
-d '{"aik":"<attacker-controlled-key>"}'
Exfiltrate Sensitive Data:
# Retrieve all registered nodes and their keys
curl https://registrar:8891/agents/
Delete Legitimate Nodes:
# Remove legitimate nodes from attestation
curl -X DELETE https://registrar:8891/agents/legitimate-uuid
What an Attacker Can Achieve
1. Bypass Attestation for Compromised Systems:
- Register compromised systems with fake measurements
- These systems will be trusted despite being compromised
- Compromised systems gain access to protected networks/data
2. Deny Service to Legitimate Systems:
- Delete legitimate node registrations
- Modify keys so legitimate nodes fail verification
- Cause widespread authentication failures
3. Exfiltrate Cryptographic Material:
- Retrieve attestation identity keys (AIKs)
- Access sensitive measurement data
- Potentially reconstruct system configurations
4. Establish Persistent Access:
- Register persistent backdoor nodes
- Modify policies to allow future compromised systems
- Disable attestation for specific critical systems
5. Lateral Movement:
- Use trusted status to access protected networks
- Leverage attestation bypass to compromise additional systems
- Escalate privileges within the environment
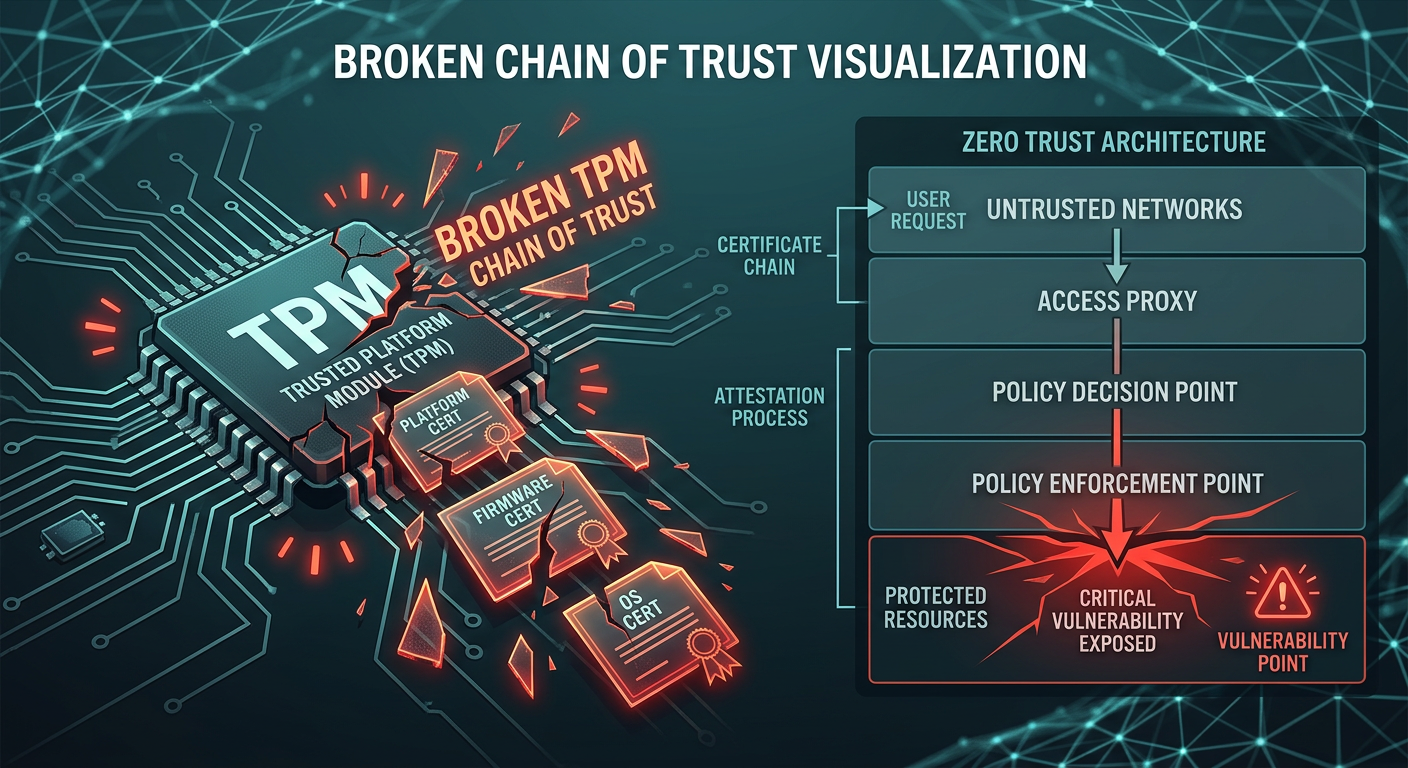
Impact on Zero-Trust Architectures
Zero Trust Depends on Attestation
Zero-trust architecture is built on the principle: “Never trust, always verify.”
A core component of “verify” is device attestation—confirming that the device requesting access is in a known-good state before granting it access to resources.
Zero-Trust Authentication Flow:
User Requests Access
↓
Identity Verified (Who are you?)
↓
Device Attested (What are you running?) ← KEYLIME PROVIDES THIS
↓
Context Evaluated (Where/When are you accessing from?)
↓
Policy Decision (Grant/Deny)
When Attestation Fails: If the attestation layer can be bypassed, the entire zero-trust model collapses. An attacker with compromised credentials can:
- Present as a trusted device (fake attestation)
- Pass identity verification (stolen credentials)
- Bypass context checks (trusted device from expected location)
- Gain access to protected resources
The Compliance Implications
Organizations using Keylime are typically doing so to meet stringent compliance requirements:
NIST 800-207 (Zero Trust Architecture): Requires “continuous verification” of device health and integrity. CVE-2026-1709 means verification can be bypassed, failing to meet NIST requirements.
NIST 800-53 (Security Controls): Multiple controls depend on attestation:
- SI-7 (Software Integrity): Requires verification of software integrity
- CM-3 (Configuration Control): Requires verification of system configuration
- IA-3 (Device Identification): Requires cryptographic device authentication
FedRAMP High Baseline: Requires hardware-rooted cryptographic verification for high-impact systems. Compromised attestation infrastructure fails to meet FedRAMP requirements.
DoD Security Technical Implementation Guides (STIGs): Multiple STIGs require TPM-based attestation. Vulnerable Keylime implementations don’t meet STIG requirements.
Industry-Specific Requirements:
PCI DSS v4.0:
- Requirement 2.2.7: System hardening verification
- Requirement 5.3.2: Detection of unauthorized changes
- Compromised attestation fails these requirements
HIPAA Security Rule:
- 164.312(a)(1): Access control with device identification
- 164.312(b): Audit controls requiring integrity verification
- Vulnerable attestation undermines these controls
CMMC Level 3:
- AC.L2-3.1.20: External system connections must be monitored
- SI.L2-3.13.6: Monitor system security alerts
- Attestation bypass means monitoring is ineffective
Audit Findings and Remediation
If You Were Audited:
Likely Finding: “The organization’s zero-trust architecture depends on Keylime for device attestation. Keylime version 7.12.0 contains CVE-2026-1709, a critical authentication bypass vulnerability. This vulnerability allows unauthorized parties to register compromised devices as trusted, undermining the entire zero-trust security model. Finding: Non-compliant.”
Required Remediation:
- Immediate: Patch Keylime to version 7.12.1-11 or later
- Evidence: Documentation of patch deployment and verification
- Assessment: Forensic review to determine if vulnerability was exploited
- Compensating Controls: If exploitation occurred, demonstrate how damage was contained
Long-Term:
- Vulnerability Management: Demonstrate process for timely patching of security infrastructure
- Monitoring: Show detection capabilities for unauthorized attestation operations
- Testing: Regular security testing of attestation infrastructure
Detection and Response
Indicators of Exploitation
Log Analysis: Examine registrar logs for suspicious activity:
Unusual Client Connections:
# Look for connections without client certificates
grep "client_certificate=null" /var/log/keylime/registrar.log
Unauthorized Agent Registrations:
# Look for agent registrations from unexpected sources
grep "agent_registration" /var/log/keylime/registrar.log | \
grep -v "expected-admin-client"
Modification of Existing Agents:
# Look for changes to existing agent records
grep "agent_update" /var/log/keylime/registrar.log
Bulk Data Access:
# Look for mass retrieval of agent data
grep "GET /agents/" /var/log/keylime/registrar.log | \
awk '{print $1}' | uniq -c | sort -rn
Network Indicators:
Unexpected Connections:
- Connections to registrar port (8891) from unauthorized sources
- Connection attempts outside maintenance windows
- Connections from unexpected geographic locations (if registrar is internet-facing)
Volume Anomalies:
- Sudden spike in registrar connections
- Unusual data transfer volumes from registrar
- Repeated connection attempts (scanning behavior)
System Indicators:
Attestation Failures:
- Legitimate nodes suddenly failing attestation
- Nodes with modified or unexpected measurements passing attestation
- Newly registered nodes without corresponding provisioning activity
Forensic Artifacts:
- Unauthorized entries in Keylime database
- Modified agent records without authorized change requests
- Deleted agent records without decommissioning documentation
Incident Response Procedures
If You Suspect Exploitation:
Phase 1: Contain (Immediate)
- Isolate the registrar: Firewall rules to block new connections
- Snapshot the system: Preserve forensic evidence
- Enable enhanced logging: Capture all current activity
- Alert security team: Activate incident response procedures
Phase 2: Assess (Within 24 Hours)
- Review all logs: Identify unauthorized activity
- Inventory registered agents: Compare against authorized list
- Check for modifications: Identify altered agent records
- Identify compromised nodes: Determine which nodes may have been falsely trusted
Phase 3: Eradicate (Within 48 Hours)
- Patch Keylime: Update to patched version 7.12.1-11+
- Rotate all keys: Regenerate attestation keys for all agents
- Re-enroll all agents: Fresh registration with new keys
- Remove unauthorized entries: Clean up malicious registrations
Phase 4: Recover (Within 72 Hours)
- Verify clean state: Confirm all agents are legitimate and properly attested
- Restore service: Bring attestation system back online
- Enhanced monitoring: Increased scrutiny for signs of persistent compromise
- Test functionality: Verify attestation is working correctly
Phase 5: Lessons Learned (Within 2 Weeks)
- Forensic report: Document what happened and how
- Root cause analysis: Why wasn’t the patch applied sooner?
- Process improvements: How to prevent similar incidents
- Communication: Report to stakeholders, auditors, regulators as required
Remediation and Hardening
Immediate Remediation
Step 1: Identify Affected Systems
# Check Keylime version on all systems
keylime-registrar --version
# Or via package manager
rpm -q keylime # RHEL/CentOS/Oracle Linux
dpkg -l | grep keylime # Debian/Ubuntu
Step 2: Apply Patches
RHEL/CentOS/Oracle Linux 9:
sudo dnf update keylime --assumeyes
# Target version: keylime-7.12.1-11.el9_7.4
RHEL/CentOS/Oracle Linux 10:
sudo dnf update keylime --assumeyes
# Target version: keylime-7.12.1-11.el10_1.4
Verification:
# Confirm patch is applied
rpm -q keylime | grep 7.12.1-11
# Restart registrar service
sudo systemctl restart keylime-registrar
# Verify mTLS is enforced
sudo journalctl -u keylime-registrar -n 50 | grep -i tls
Step 3: Forensic Check
# Review recent registrar activity
sudo journalctl -u keylime-registrar --since "2 weeks ago" > registrar_audit.log
# Look for suspicious patterns
grep -E "(registration|modification|deletion)" registrar_audit.log
Long-Term Hardening
1. Network Segmentation
Isolate Attestation Infrastructure:
Management Network (10.0.1.0/24)
├─ Keylime Registrar (10.0.1.10)
├─ Keylime Verifier (10.0.1.11)
└─ Administrative Jump Box (10.0.1.100)
Firewall Rules:
- Allow 8891/tcp only from known admin IPs
- Allow 8891/tcp from verified agents only
- Deny all other inbound traffic
- Log all connection attempts
2. Enhanced Authentication
Certificate-Based Access Control:
# registrar_config.yaml
tls:
enabled: true
cert: /etc/keylime/registrar-cert.pem
key: /etc/keylime/registrar-key.pem
client_ca: /etc/keylime/client-ca.pem
client_cert_required: true # Enforce mTLS
allowed_clients:
- cn=admin-1
- cn=admin-2
3. Monitoring and Alerting
SIEM Integration:
# Example SIEM rule (pseudo-code)
rule keylime_unauthorized_access:
when:
- source: keylime-registrar
- event: agent_registration OR agent_modification
- client_certificate: null OR client_cn not in whitelist
then:
- alert: CRITICAL
- notify: security-team@org.com
- action: block_source_ip
Metrics to Monitor:
- Failed authentication attempts
- Agent registrations outside maintenance windows
- Modifications to existing agents
- Bulk data access patterns
- Connections from unexpected sources
4. Regular Security Assessments
Penetration Testing:
- Include attestation infrastructure in pentest scope
- Specifically test authentication bypass scenarios
- Verify network segmentation effectiveness
Configuration Audits:
- Quarterly review of Keylime configurations
- Verify mTLS is enforced
- Check for configuration drift
Vulnerability Management:
- Subscribe to Keylime security advisories
- Monitor CVE databases for Keylime mentions
- Emergency patching procedures for critical vulnerabilities
Strategic Recommendations for Compliance Teams
1. Treat Trust Infrastructure as Critical
The Mindset Shift: Attestation and PKI infrastructure is often treated as secondary to production systems. CVE-2026-1709 demonstrates that compromised trust infrastructure undermines all downstream security.
Actions:
- Inventory trust infrastructure: Keylime, PKI, certificate authorities, HSMs
- Classify as Tier 1 critical: Same priority as production databases and authentication systems
- Dedicated security focus: Regular security reviews and testing
- Incident response priority: Trust infrastructure incidents get highest priority
2. Understand Your Supply Chain
The Realization: You depend on Keylime (and many other open-source projects) for security-critical functions. Do you understand:
- Who maintains the project?
- What security review process exists?
- How vulnerabilities are disclosed and patched?
- What your response process is for upstream vulnerabilities?
Actions:
- Map dependencies: Document all security-critical open-source projects
- Monitor security advisories: Subscribe to all relevant sources
- Contribute upstream: Consider contributing to projects you depend on
- Have alternatives: Understand what you’d do if a project fails or is compromised
3. Design for Trust Infrastructure Failure
Assume Breach Extends to Trust Infrastructure: Zero-trust architecture assumes systems may be compromised. CVE-2026-1709 shows that trust infrastructure itself can be compromised.
Defense in Depth Beyond Attestation:
- Network segmentation: Limit blast radius even if attestation is bypassed
- Behavioral monitoring: Detect anomalies even in “trusted” systems
- Principle of least privilege: Limit what trusted systems can access
- Regular re-attestation: Continuous verification, not one-time
- Multiple trust anchors: Don’t depend solely on Keylime attestation
Actions:
- Architecture review: Identify single points of trust failure
- Layered controls: Implement multiple independent security controls
- Monitoring redundancy: Multiple detection mechanisms
- Regular testing: Red team exercises targeting trust infrastructure
4. Compliance as Risk Management, Not Checkbox Exercise
The Compliance Question: Is an organization compliant if they implement all required controls, but a critical vulnerability in the control infrastructure makes those controls ineffective?
The Better Approach:
- Risk-based compliance: Focus on actual risk reduction, not just control implementation
- Continuous assessment: Compliance is ongoing, not point-in-time
- Vulnerability management integration: Compliance status changes when vulnerabilities are discovered
- Transparent reporting: Disclose security incidents affecting compliance posture
Actions:
- Update compliance procedures: Include vulnerability management in compliance assessments
- Define acceptable risk: What level of vulnerability risk is acceptable before losing compliance?
- Remediation timelines: How quickly must critical vulnerabilities be patched?
- Compensating controls: What temporary controls can maintain compliance during remediation?
Lessons Learned: The Meta-Security Problem
CVE-2026-1709 highlights a fundamental challenge in cybersecurity: How do we secure the systems that provide security?
The Recursive Trust Problem
The Chain of Trust:
Hardware (TPM)
↓ trusts
Firmware
↓ trusts
Bootloader
↓ trusts
Operating System
↓ trusts
Keylime Agent
↓ trusts
Keylime Registrar ← VULNERABILITY HERE
↓ trusts
Keylime Verifier
↓ trusts
Access Control System
When a link in this chain breaks, everything downstream is compromised.
The Meta-Question: If your attestation system is compromised, how do you attest to its compromise? You can’t use the compromised attestation system to verify itself.
The Open Source Security Challenge
The Paradox:
- Open source is more secure because code is transparent and reviewed by many eyes
- Open source is less secure because volunteer maintainers may miss vulnerabilities
Keylime’s Context:
- CNCF project with security focus
- Used in high-assurance environments
- Critical security function
- Yet a major authentication bypass shipped in production
The Reality: Even well-intentioned, security-focused open-source projects can have critical vulnerabilities. The solution isn’t to avoid open source—it’s to:
- Support projects financially: Enable proper security review
- Contribute security expertise: Help with security audits and testing
- Deploy defense in depth: Don’t depend solely on any single security control
- Monitor vulnerabilities: Rapid response when issues are discovered
Conclusion: Trust, Verify, and Monitor
CVE-2026-1709 in Keylime serves as a stark reminder that trust infrastructure can fail, and when it does, the consequences cascade through your entire security architecture.
Key Takeaways:
✅ Zero trust requires trusted verification mechanisms – When attestation can be bypassed, zero trust collapses
✅ Trust infrastructure is critical infrastructure – Treat it with the same priority as production systems
✅ Defense in depth extends to trust infrastructure – Don’t depend solely on attestation
✅ Vulnerability management is compliance – Critical vulnerabilities affect compliance posture
✅ Monitoring trust infrastructure is essential – You need to detect when trust mechanisms are compromised
For Compliance Officers:
📋 Immediate: Verify Keylime is patched if deployed
📋 Short-term: Review all trust infrastructure for vulnerabilities
📋 Long-term: Implement continuous trust infrastructure monitoring and testing
For Security Architects:
🏗️ Design for trust infrastructure failure – What happens if attestation is bypassed?
🏗️ Implement layered verification – Multiple independent trust mechanisms
🏗️ Monitor attestation operations – Detect unauthorized attestation modifications
For Risk Managers:
⚠️ Assess trust infrastructure risk – Map dependencies and single points of failure
⚠️ Define risk appetite – What vulnerability severity requires emergency response?
⚠️ Plan for worst case – What if attestation was compromised without detection?
The Ultimate Lesson:
In zero trust, we say “never trust, always verify.” CVE-2026-1709 reminds us that we must also verify our verification mechanisms—and have plans for when they fail.
Because in security, it’s not about whether trust infrastructure will be compromised. It’s about detecting it quickly, responding effectively, and limiting the damage when it inevitably happens.
Additional Resources
Technical Documentation:
- Keylime Documentation: https://keylime.dev/
- Red Hat Advisory RHSA-2026:2224 and RHSA-2026:2225
- CISA Vulnerability Bulletin SB26-040
Compliance Guidance:
- NIST 800-207: Zero Trust Architecture
- NIST 800-53 Rev 5: Security and Privacy Controls
- NIST 800-155: BIOS Integrity Measurement Guidelines
Implementation Resources:
- Keylime Deployment Guide
- TPM 2.0 Best Practices
- Remote Attestation Architecture Patterns
Security Research:
- A Hitchhiker’s Guide to Remote Attestation (Keylime blog)
- TPM-Based Continuous Attestation (academic paper)
- Zero Trust Reference Architecture (Microsoft/Google)
This article is based on the CVE-2026-1709 disclosure, Red Hat security advisories, CISA bulletins, and technical documentation from the Keylime project. Organizations using Keylime should consult directly with their security vendors and the Keylime community for deployment-specific guidance.